
Hackers Bypass Built-in Windows Protections
Recent news from the cybersecurity realm reveals that hackers have found a way to bypass the built-in protections of the Windows operating system. This vulnerability, discovered by researchers, allows malicious actors to circumvent security mechanisms designed to protect users from malware and attacks. It's crucial to note that such threats can jeopardize user data and information security.
Continue reading
The Resurgence of Dormant Mac Malware: New Capabilities for Hackers
Recent reports about a long-dormant Mac malware, known as Gimmick, have caught the attention of cybersecurity experts. This malicious software was thought to be lost and had been virtually invisible to users. However, its unexpected return to cyberspace has resulted in updated capabilities, allowing hackers to more effectively target Mac devices.
Continue reading
What to Do if Your Social Media Has Been Hacked: A Comprehensive Guide
In today's digital world, social media security has become critically important, especially following recent hacking incidents. Panic has spread among users as news of massive data leaks and account compromises emerged on popular platforms. The new information highlighting how hackers gained access to personal information and even used it for malicious purposes underscores the necessity for active surveillance of your account security.
Continue reading
Hackers Hijack Subaru Starlink: A Security Threat for Drivers
Recently, serious vulnerabilities in the Subaru Starlink system were revealed, allowing hackers to gain remote access to vehicles, posing a threat to the safety of drivers and passengers. Cybersecurity researchers discovered that criminals could easily exploit weaknesses related to the Starlink API. The Starlink system, designed to support and control vehicle functions through a mobile application, found itself unexpectedly under threat.
Continue reading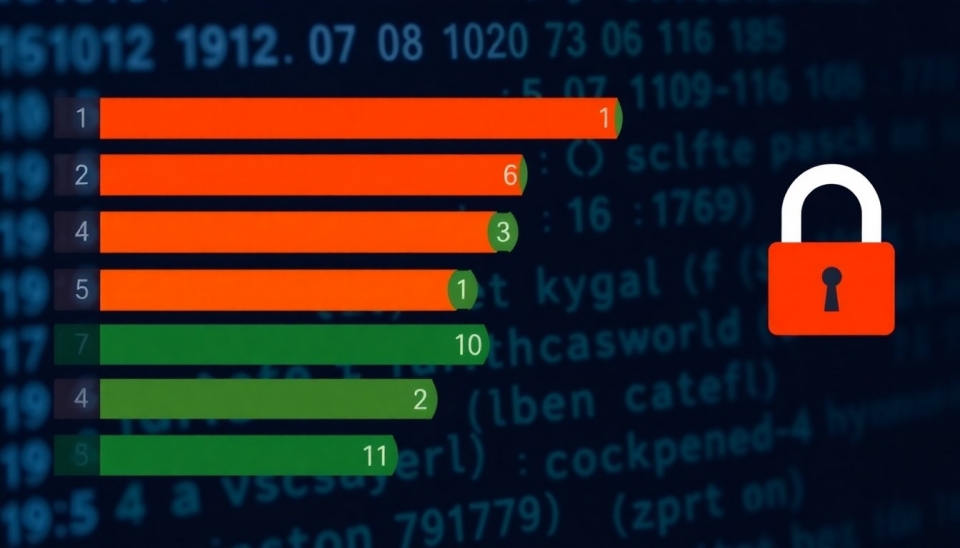
The Top 10 Most Popular and Worst Passwords of 2024: What You Need to Know for Your Security
In 2024, cybersecurity experts are once again presenting the most commonly used and unsafe passwords that users continue to employ, despite repeated recommendations to change them. The study revealed that the frequently used passwords have not changed from previous years, with many users sticking to simple, easily guessable combinations.
Continue reading
Scam Tricks Targeting Teens: How Fraudsters Use the Internet to Deceive
In today's world, online fraud is taking on more sophisticated forms, and scammers are now turning their attention to teenagers, employing various nasty tricks to manipulate and deceive them. These schemes are becoming more prevalent as teenagers increasingly engage with technology and social media.
Continue reading
T-Mobile Telecom Company Suffered Major Cyber Attack from Chinese Hackers
Recent events have highlighted the vulnerability of major U.S. telecommunications companies, as it has been revealed that T-Mobile, one of the country's leading cellular operators, fell victim to a large-scale attack associated with cyber espionage carried out by Chinese hackers. This event has drawn attention to the sobering reality that many companies face in light of increasing threats in cyberspace.
Continue reading
The Google Meet Issue: How Sneaky Errors Become a Hacker's Trap
Recent reports regarding glitches in Google Meet, the video conferencing platform, have drawn attention not just from users but also from cybersecurity experts. This issue gains traction after it was revealed that some of these glitches could be exploited not just for creating disruptions but also for injecting malware. The situation arises amid growing concerns over cyber threats that could jeopardize personal safety and the overall reliability of the platform.
Continue reading